The advent of computers and the Internet has provided numerous benefits to humanity. Indeed, these technologies have transformed the manners through which people transact business, obtain their education, communicate with one another, manage their health and finances, undertake research and even the means through which governments engage with constituents, among many other things. Indeed, through the widespread use of the Internet, consumers are now increasingly conducting their businesses online in what is now known as e-commerce. Unfortunately, just as the Internet and computers may be harnessed for progressive activities, these technologies have also become useful tools for malicious entities so that they could perpetrate their unlawful acts, including, online fraud.
Online fraud refers to deceptive behaviour that is perpetrated over the Internet in an illegal manner. Based on this definition, online fraud constitutes a broad range of activities that include theft of proprietary information through hacking; credit card fraud; identity theft; scamming; auction site fraud; lottery scams; cheque overpayments; false websites and advanced fee fraud. The most common motive for perpetrating online fraud is for economic gain. The adverse impacts of online fraud include monetary, loss of control over certain business processes, loss of trust between consumer and provider as well as loss of interest in e-commerce which is the source of livelihood for millions of people across the globe.
In the Kingdom of Saudi Arabia (KSA), SR16 billion is lost to commercial fraud each year, with an increasing proportion attributed to online fraud. Moreover, whereas e-commerce in KSA is not as advanced in comparison to the United States or China, e-commerce is poised to exponentially grow due to the increasing ubiquity of the Internet and smartphones in the Kingdom. Indeed, the Saudi Ministry of Trade and Industry and the Saudi Interpol had long issued warnings about the dramatic increase in cases of Internet fraud in KSA.
PURPOSE OF THE STUDYThe proposed study seeks to determine the various measures that the KSA could prevent online fraud. The underlying rationale here is that online fraud exacts significant costs to consumers, businesses as well as the national economy, such that it has to be urgently addressed just like any illegal act. In light of these, the specific objectives of the proposed study are to:
1. Conduct a comparative case study on the KSA and the United Kingdom in terms of addressing the problem of online fraud.
2. Extract from this comparative case study important lessons that the KSA may learn from the experience of the United Kingdom.
Moreover, the proposed study seeks to answer these research questions:
1. How can online fraud in the KSA be prevented through legislative means?
2. How can online fraud in the KSA be prevented through the use of the human-computer interaction approach?
3. What are the security measures that online businesses can adopt to ensure that online fraud is prevented?
THE CONTEXTThe United Kingdom aggressively battles online fraud through legislation and other support systems. This is because online fraud in the United Kingdom has generated monetary costs amounting to billions of pounds such that the government wanted to address the problem once and for all through legislative measures. For instance, online banking fraud alone in 2008 cost British banks £39 million, reflecting an increase of 55% from a year earlier. Identity fraud cost the British economy an average of £1.2 billion annually, or £25 for every adult in the United Kingdom. Consequently, the United Kingdom enacted a number of laws including, the Computer Misuse Act (1990), as amended by the Police and Justice Act and the Fraud Act. The United Kingdom also created special agencies such as the National Hi-Tech Crime Unite and the Police Central e-Crime Unit. In contrast, the KSA continues to face barriers in addressing online fraud because of "a lack of clear regulations and support systems" (Arab News). Such support systems include HCI and information security capabilities.
METHODOLOGYThe proposed study will use the comparative case study design. To note, the comparative case study has three objectives. First, it aims to systematically analyze covariations between two or more cases in order to identify causal relationships (Collier 1993). Second, it investigates at least two cases for the purpose of determining a specific framework or set of concepts that are material to the cases. Third, it seeks to investigate at least two cases so that the researcher can highlight the degree to which they are different from one another so that ultimately, it becomes possible to establish a framework for the interpretation of "parallel processes of change that are played out in different ways within the context" (Collier). Thus, the KSA and the United Kingdom experiences with online fraud will be investigated for the proposed study, with lessons learned from the United Kingdom to be analyzed for adoption in the KSA.
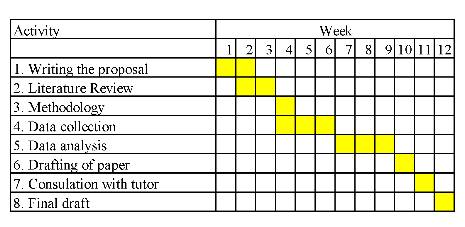 Proposed Time FrameEXPECTATIONS
Proposed Time FrameEXPECTATIONSAt this point, it is expected that legislation alone will not be able to address the problem of online fraud in the KSA. Thus, the importance of HCI and security measures is emphasized.
ReferencesAgourram, H., Robson, B., & Nehari-Talet, A. (2006). Succeeding the implementation of e-learning systems in a multicultural environment. International Journal of Learning, 13(3), 89-96.
Al-Fahad, F. N. (2010). The learners' satisfaction toward online e-learning implemented in the College of Applied Studies and Community Service, King Saud University, Saudi Arabia: can e-learning replace the conventional system of education? Turkish Online Journal of Distance Education (TOJDE), 11(2), 61-72.
Al-Mobaideen, H. O., Al-Bashabsheh, S. A., Basioni, E., & al-khawaldeh, A.
Electronic government services and benefits in Jordan. International Journal of Academic Research, 5(6), 206-215. doi:10.7813/2075-4124.2013/5-6/A.26.
Al-Somali, S., Gholami, R., & Clegg, B. (2009). An investigation into the acceptance of online banking in Saudi Arabia. Technovation, 29(2), 130-141.
doi:10.1016/j.technovation.2008.07.004
Arab News. (2013). KSA loses SR16bn in commercial fraud.
Bauerly, R. J. (2009). Online auction fraud and eBay. Marketing Management Journal, 19(1), 133-143.
Chung, W., Chen, H., Chang, W., & Chou, S. (2006). Fighting cybercrime: a review and the Taiwan experience. Decision Support Systems, 41(3), 669-682.
doi:10.1016/j.dss.2004.06.006
Hache, A., & Ryder, N. (2011). 'Tis the season to (be jolly?) wise-up to online fraudsters.
Criminals on the Web lurking to scam shoppers this Christmas: a critical analysis of the United Kingdom's legislative provisions and policies to tackle online fraud. Information & Communications Technology Law, 20(1), 35-56. doi:10.1080/13600834.2011.557537
Levi, M., & Burrows, J. (2008). Measuring the impact of fraud in the UK. British Journal of Criminology and Academic Studies, 48(3), 293-318. doi:10.1093/bjc/azn001
Molla, A., & Heeks, R. (2007). Exploring e-commerce benefits for businesses in a developing country. Information Society, 23(2), 95-108. doi:10.1080/01972240701224028
Mohatar, O., & Sierra Cámara, J. M. (2007). New directions in online fraud. AIP Conference Proceedings, 963(2), 973-976. doi:10.1063/1.2836255
Narayanan, M., Koo, B., & Cozzarin, B. (2012). Fear of fraud and Internet purchasing. Applied Economics Letters, 19(16), 1615-1619. doi:10.1080/13504851.2011.648313
Saudi Gazette. (2012). Saudi Interpol warns of Internet fraud.
Sears Campbell, D. (2002). Focus on cyber-fraud. Internal Auditor, 59(1), 28.
Simpson, L. L. (2006). Watchdogs on the Internet - protecting consumers against online fraud. Advances in Consumer Research, 33(1), 303-304.
Standing, C., & Chad, L. (2007). Organizational evaluation of the benefits, constraints, and satisfaction of business-to-business electronic commerce. International Journal of Electronic Commerce, 11(3), 107-134. doi:10.2753/JEC1086-4415110304
UPI. (2005). Internet fraud rises in Saudi Arabia. University research.


